Identity and Access Security based on Zero Trust
Have total control and visibility over who accesses your data, systems, applications, infrastructure and any other assets, preventing cyber attacks and data breaches. With VaultOne, protect your company’s resources and achieve compliance. Where PAM meets IGA with an IAM twist!
Clients
Improve privileged access management with VaultOne
We’re trusted by more than 55,000 professionals daily.







Zero Trust
The right privilege at the right time, with control and visibility

VaultOne is redesigning the concept of privileged access management (PAM). Manage user access, credentials and sessions in a fast, secure and automated way. In a single and powerful solution, we offer multiple features, such as digital vault, password generator, sessions recording, auditing and reporting, customizable policies, disaster recovery and multi-factor authentication.
Total Protection
VaultOne's access security features
If you’re looking for a solution to protect shared accounts, certificates and user access to applications, websites, servers, databases, cloud services and infrastructure, you’ve just found it.
Access manager capabilities allow you to secure user access, especially remote access, defending your sensitive data and resources against attacks and unauthorized access.
Monitor, record and control privileged session activity, protecting your data, users, resources and assets.
Easily and securely manage your business’s passwords, credentials and certificates.
Store your passwords in a secure solution protected by encryption and define who can access them.
Automate security and administration tasks, ensuring better protection and more agility, giving you and your team more time to focus on other activities.
Add an extra layer of protection with multi-factor authentication whenever a user requests access to your company’s resources and assets.
Meet security and privacy compliance requirements, such as GDPR and ISO 27001, by implementing least privilege access and being able to identify all of your users and privileged accounts (your team and third parties).
Use the role-based administration feature to create and define granular administrative roles, giving users only the tools and permissions they need to get the job done.
Create customizable policies according to your company’s demands so that they help you ensure data, resources, and systems protection.
Have access to your resources and assets whenever you need, since our solution is designed with failover safeguards, ensuring real availability.
Why VaultOne
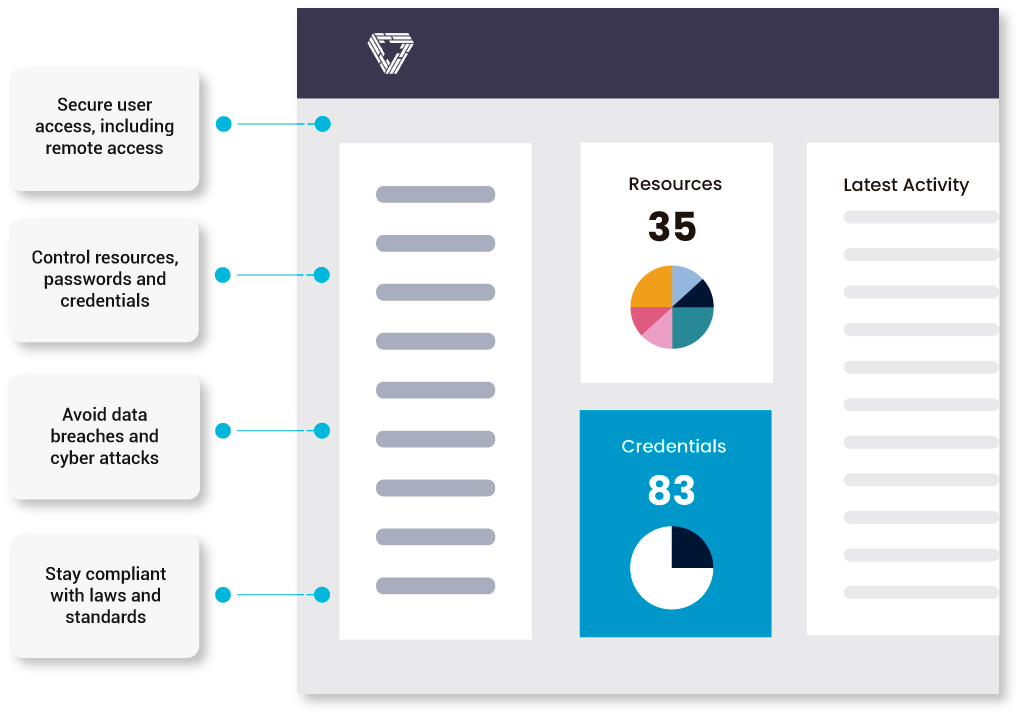
We help to protect your business in many ways
Secure user access, for your team and third-party users
Avoid cyber attacks, human errors, and data breaches
By creating customized access policies and managing users and privileges, you fight cyber attacks and avoid data breaches.
Secure your cloud and hybrid environments
Audit and control user access, and achieve compliance
Audit and control access to assets and data, ensuring compliance with GDPR, ISO 27001, HIPPA, PCI, SOX and FIPS.
- Easy to Manage and Deploy
- Flexibility and Scalability
- Fair and Competitive Price
- Top-level Support
- Privacy and Security by Design
- Advanced Technology
Hear Our Customers
Customer reviews


